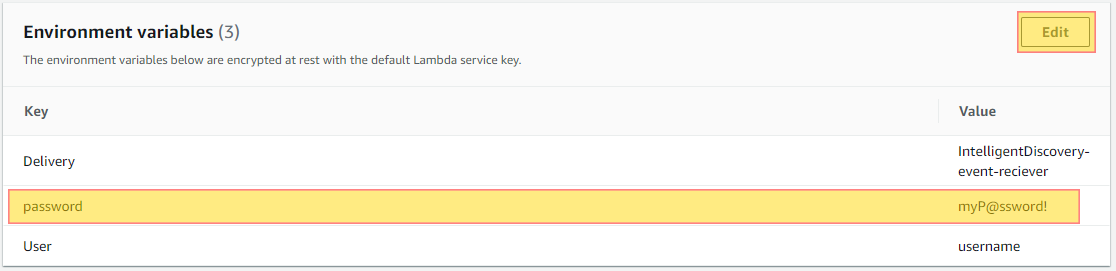
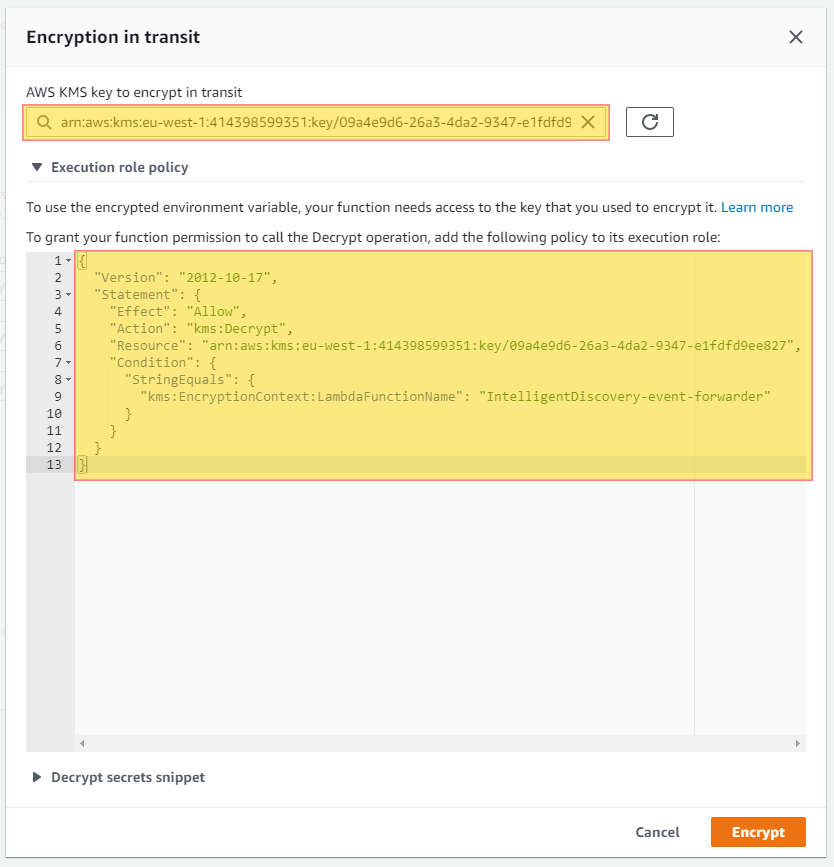
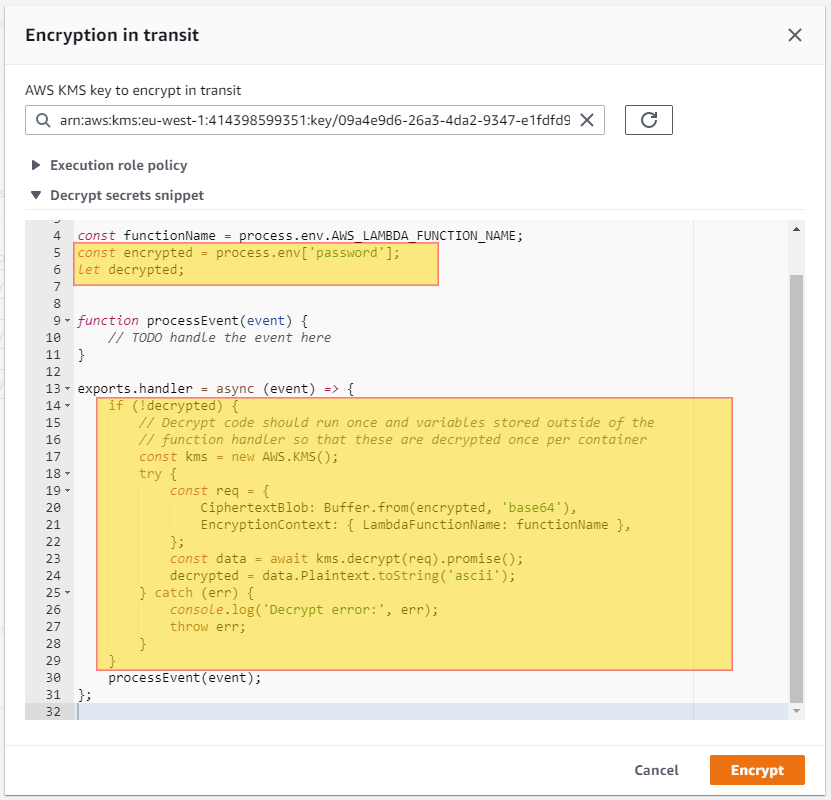
Ensure that your Lambda functions environment variables are not exposing sensitive data such as passwords, data base connection strings, aws access keys and such. Understanding that anyone that has read only access to your AWS account has the ability to read what has been set in these variables.s For this reason this is considered a security best practice and should have all sensitive data encrypted via KMS. Ensuring this is enabled will help you with HIPPA, GDPR and NIST compliance.
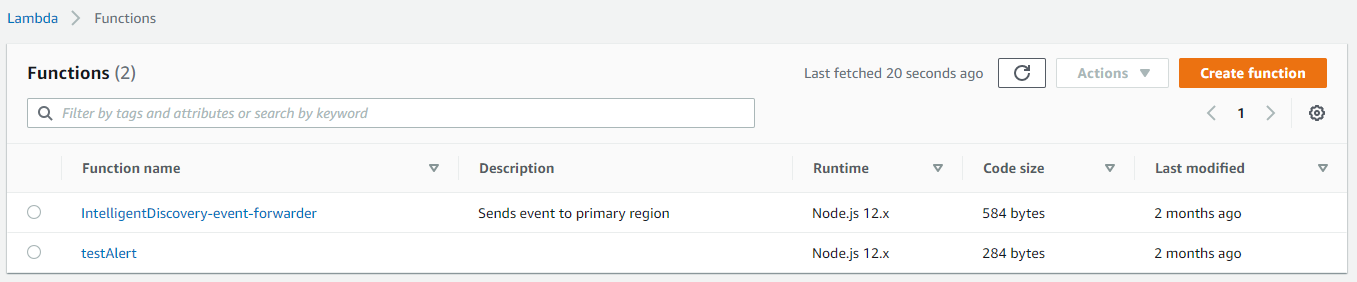
Do you want to see all of your Lambda Functions in once place for all regions and all accounts?
Login to our online demo to see exactly what this looks like.
demo.intelligentdiscovery.io
Consolidate your inventory management with consistent and frequent security logs, inventories, and change logs. Dashboard reporting for extensive analytical value.
learn more +Access consolidated capacity, cost, and volume tools in a scaling environment without impacting production or breaking the bank.
learn more +