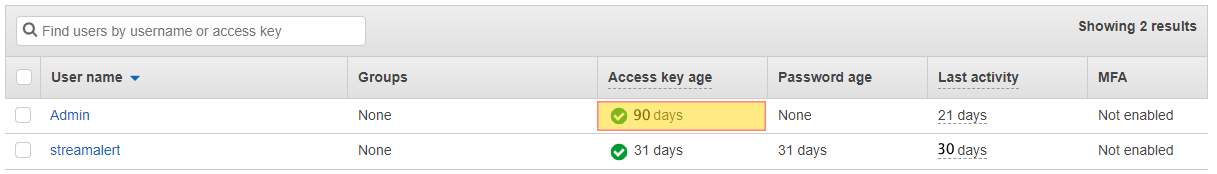
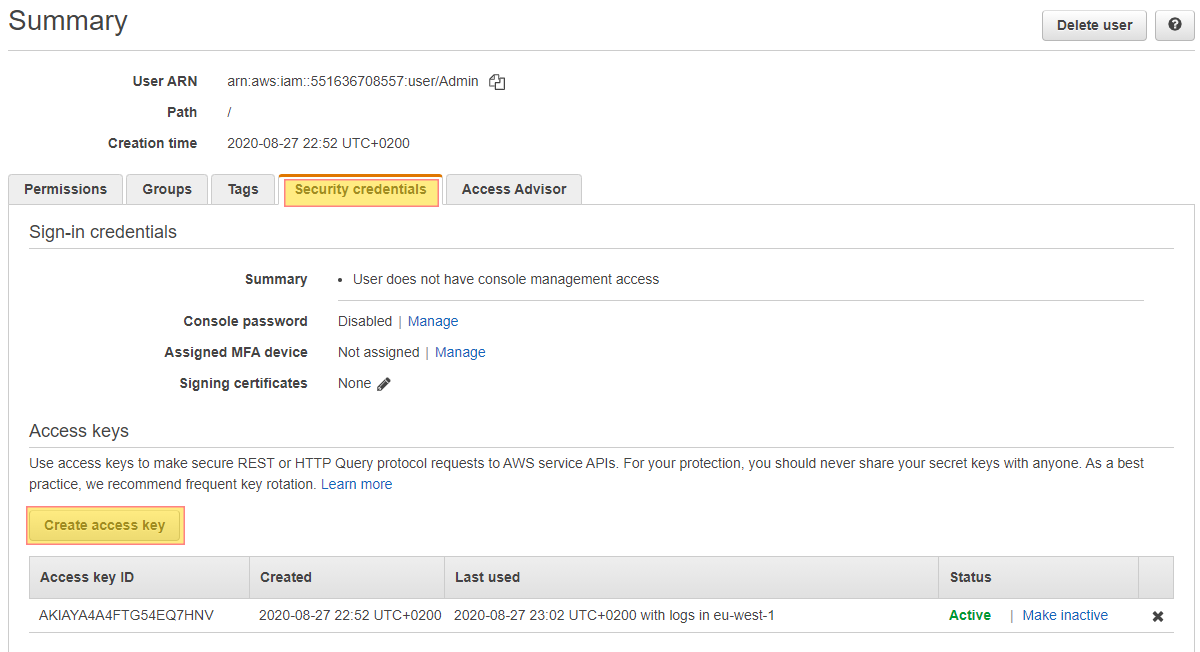
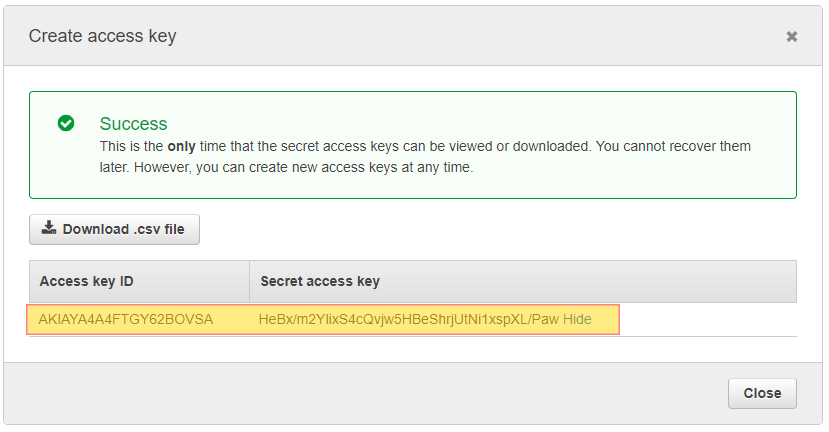
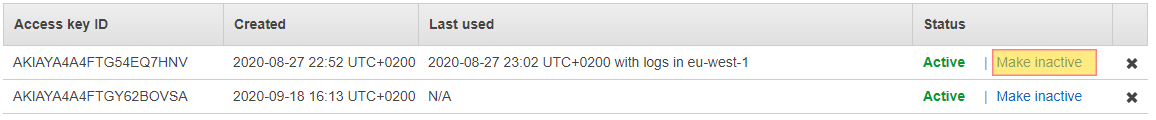
IAM access keys work as credentials for programmatic access. Credentials should be rotated or changed on a periodic time frame. For this reason it is considered a security best practice to rotate access keys. Ensuring that your account is restricted with MFA will help you with CIS and NIST Compliance.
Do you want to see all of your AWS EC2 Instances in once place for all regions and all accounts?
Login to our online demo to see exactly what this looks like.
demo.intelligentdiscovery.io
Consolidate your inventory management with consistent and frequent security logs, inventories, and change logs. Dashboard reporting for extensive analytical value.
learn more +Access consolidated capacity, cost, and volume tools in a scaling environment without impacting production or breaking the bank.
learn more +