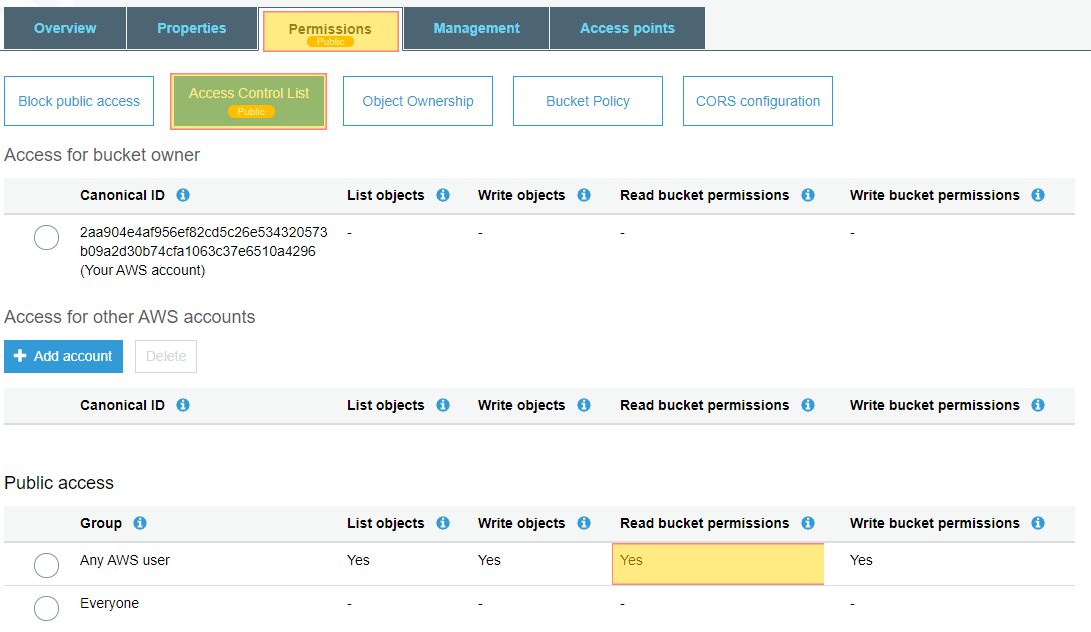
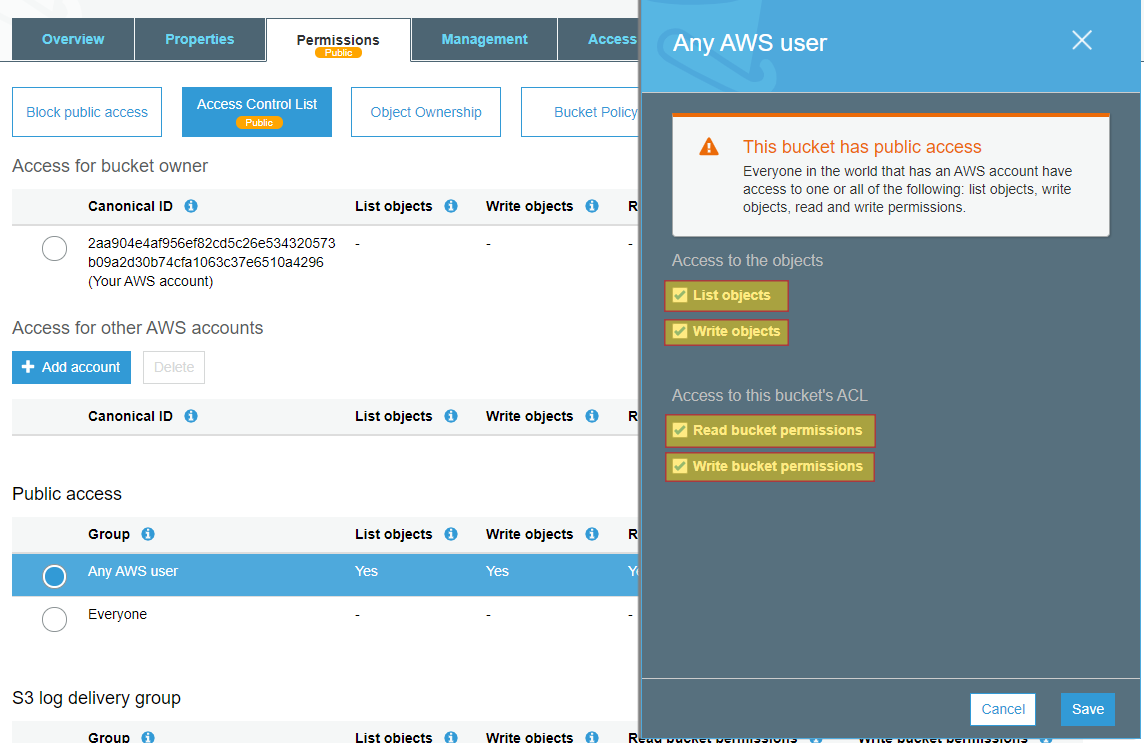
Ensure that your S3 buckets are not exposed to allow aws authenticated users to have read ACP access on your buckets. This is considered security best practice and should always be done. Ensuring this is enabled will help with NIST,HIPPA, GDPR and PCI-DSS compliance.
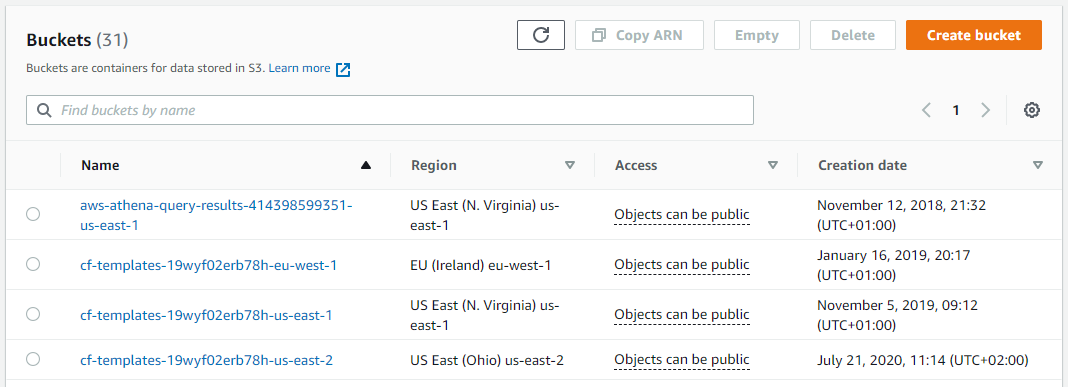
Do you want to see all S3 Buckets in once place for all regions and all accounts?
Login to our online demo to see exactly what this looks like.
demo.intelligentdiscovery.io
Consolidate your inventory management with consistent and frequent security logs, inventories, and change logs. Dashboard reporting for extensive analytical value.
learn more +Access consolidated capacity, cost, and volume tools in a scaling environment without impacting production or breaking the bank.
learn more +